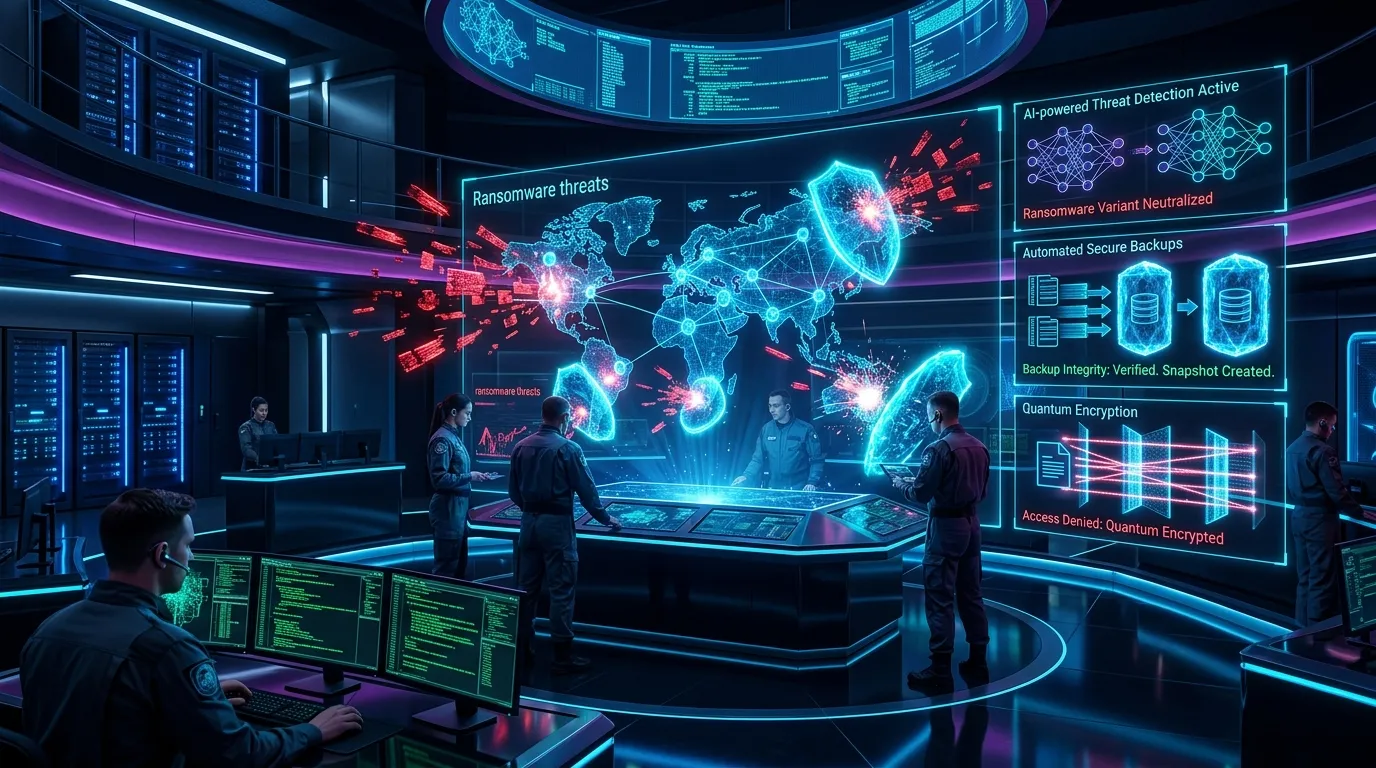
Ransomware remains one of the most disruptive cyber threats facing organizations worldwide. What began as opportunistic malware targeting individual users has evolved into a highly organized, financially motivated criminal enterprise. Modern ransomware attacks are strategic, targeted, and often executed by coordinated groups using advanced tactics.
Attackers no longer rely solely on encrypting files and demanding payment. Many campaigns now involve double extortion techniques — encrypting systems while also exfiltrating sensitive data. Victims face pressure not only to restore operations but also to prevent public data leaks.
The financial and reputational consequences of ransomware incidents have prompted organizations to strengthen defense strategies. Cybersecurity is no longer focused solely on prevention; it also emphasizes rapid detection, containment, and recovery.
Security firms such as CrowdStrike and Sophos provide advanced endpoint protection and incident response services designed to mitigate ransomware risk.
Modern ransomware defense strategies revolve around several core pillars:
- Proactive threat detection
- Network segmentation
- Robust backup and recovery systems
- Employee awareness training
- Incident response planning
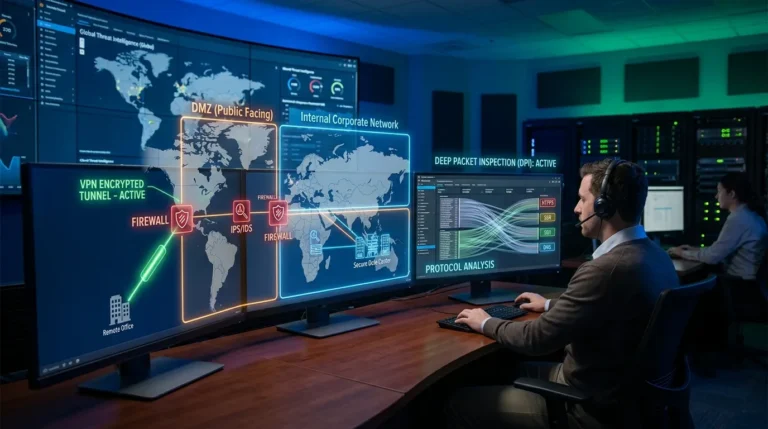
Proactive detection involves continuous monitoring of endpoints and network traffic. Behavioral analytics tools identify suspicious activity, such as unusual file encryption patterns or unauthorized privilege escalation.
Network segmentation limits lateral movement within systems. If attackers gain access to one part of the network, segmentation restricts their ability to spread across critical systems.
Backup strategies are essential for resilience. Secure, offline backups ensure that encrypted data can be restored without paying ransom demands. Regular testing of backup integrity strengthens recovery readiness.
Human error continues to serve as a common entry point. Phishing emails frequently deliver ransomware payloads. Employee training programs help reduce susceptibility to social engineering attacks.
Cloud environments introduce both risks and opportunities. As organizations migrate workloads to platforms like Microsoft Azure and Amazon Web Services, they benefit from built-in redundancy and monitoring tools. However, misconfigured cloud storage can expose sensitive data.
Incident response planning has become a strategic necessity. Organizations are developing playbooks outlining roles, communication protocols, and containment procedures in the event of an attack.
Ransomware groups increasingly operate under “ransomware-as-a-service” models, lowering the barrier to entry for cybercriminals. This trend increases attack frequency and sophistication.
Encryption alone is no longer the only threat. Data theft and public disclosure amplify pressure on victims. As a result, organizations are investing in data loss prevention (DLP) technologies to detect unauthorized exfiltration.
Key challenges in ransomware defense include:
- Rapidly evolving attack techniques
- Targeted attacks against critical infrastructure
- Third-party supply chain vulnerabilities
- Balancing business continuity with containment
Cyber insurance policies often require demonstration of robust security controls before coverage approval, further incentivizing defensive investments.
Industry analysts emphasize that resilience, rather than absolute prevention, defines modern ransomware defense. No system can guarantee immunity from attack, but layered security and rapid recovery capabilities significantly reduce impact.
The integration of artificial intelligence enhances detection speed, identifying ransomware behaviors within seconds of execution.
Organizations are also collaborating across industries to share threat intelligence, strengthening collective defense capabilities.
Ransomware defense strategies continue evolving as threat actors refine tactics. Enterprises that prioritize proactive monitoring, strong backups, and incident readiness position themselves to withstand disruptions more effectively.
In the current threat landscape, preparedness and resilience define cybersecurity maturity. Ransomware may remain persistent, but strategic defense frameworks ensure organizations can recover swiftly and protect long-term operational stability.