As digital ecosystems expand across cloud platforms, remote devices, and SaaS applications, identity has emerged as the new security perimeter. Organizations are increasingly prioritizing Identity and Access Management (IAM) as a foundational pillar of cybersecurity strategy.
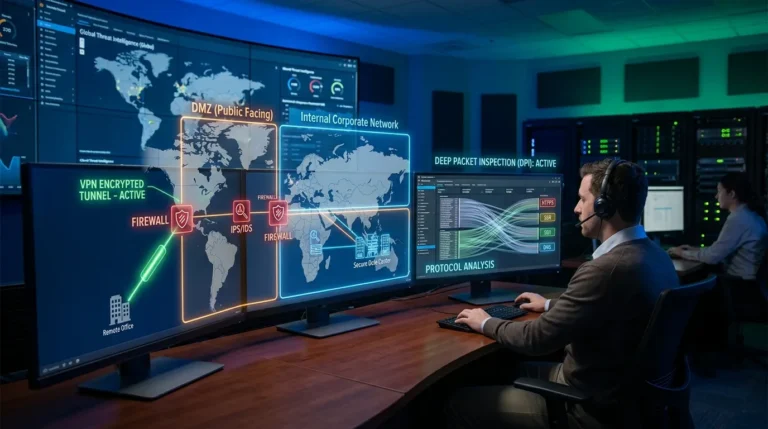
In traditional IT environments, security focused on protecting network boundaries. Today, with distributed workforces and cloud-native architectures, network perimeters are no longer clearly defined. Employees, contractors, partners, and automated systems access enterprise resources from diverse locations and devices.
Identity management systems ensure that only authorized users gain access to sensitive applications and data. Rather than relying on implicit trust based on location, modern security models validate identity continuously.
Major technology providers such as Microsoft and Okta offer enterprise-grade identity platforms that centralize authentication and enforce granular access controls.
Core components of modern IAM strategies include:
- Multi-factor authentication (MFA)
- Single sign-on (SSO)
- Role-based access control (RBAC)
- Privileged access management (PAM)
- Continuous authentication monitoring
Multi-factor authentication significantly reduces the risk of credential-based attacks. By requiring additional verification factors beyond passwords, organizations limit unauthorized access even if credentials are compromised.
Single sign-on simplifies user experience while maintaining security. Employees authenticate once and gain access to multiple systems through secure token exchanges.
Privileged access management has become particularly critical. Administrative accounts with elevated privileges present high-value targets for attackers. PAM solutions restrict and monitor privileged sessions, reducing risk exposure.
Cloud adoption further elevates IAM importance. Platforms such as Amazon Web Services rely heavily on identity policies to regulate resource access. Misconfigured identity roles can expose entire cloud environments.
Zero Trust security frameworks integrate closely with IAM systems. Every access request is validated based on identity, device status, and contextual risk factors.
Behavioral analytics enhances IAM effectiveness. Systems analyze login patterns and flag unusual activity, such as logins from unfamiliar geographic locations or unexpected times.
Despite technological advancements, challenges persist.
Password fatigue remains common. Users managing multiple credentials may adopt insecure practices, such as password reuse.
Third-party access management introduces additional complexity. Vendors and contractors require controlled access without compromising security.
Key challenges in IAM implementation include:
- Managing identity across multi-cloud environments
- Balancing security with user convenience
- Monitoring privileged account activity
- Integrating legacy systems
- Ensuring regulatory compliance
Automation supports IAM scalability. Automated provisioning and de-provisioning of accounts ensure that access aligns with employment status changes.
Compliance frameworks increasingly require strict identity controls. Regulations governing financial and healthcare data demand robust authentication mechanisms.
Industry analysts note that identity-based attacks are among the most common intrusion vectors. Strengthening IAM directly reduces breach probability.
As organizations expand digital services and remote work models, identity governance becomes central to cybersecurity resilience.
IAM is no longer a supporting tool within security architecture — it is a strategic control layer protecting distributed digital ecosystems.
By embedding identity verification into every access interaction, enterprises reinforce trust and reduce risk across cloud, on-premise, and hybrid environments.
In a borderless digital landscape, identity is the foundation upon which secure operations are built.