As organizations accelerate cloud adoption, security experts continue to highlight a persistent vulnerability: cloud misconfigurations. While cloud platforms provide robust native security controls, improper configuration of services remains one of the most common causes of data exposure and security incidents.
Cloud environments are inherently complex. Enterprises deploy virtual machines, storage buckets, databases, APIs, and containerized applications across multiple regions and accounts. Each component requires specific access permissions, encryption settings, and network policies. A single overlooked configuration can expose sensitive data to unauthorized access.
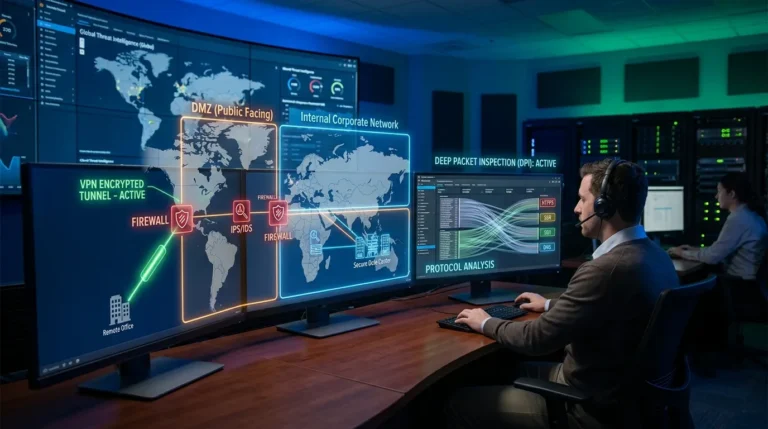
Major cloud providers such as Amazon Web Services and Microsoft Azure operate under a shared responsibility model. Providers secure the underlying infrastructure, but customers are responsible for configuring applications, identity policies, and data protections correctly.
Misconfigurations frequently involve:
- Publicly accessible storage buckets
- Overly permissive identity and access roles
- Disabled encryption settings
- Open network ports
- Inadequate logging and monitoring
One of the most common incidents involves storage services configured for public access without proper authentication controls. Sensitive data, including customer information and proprietary business documents, can become exposed unintentionally.
Identity and access management (IAM) errors also create vulnerabilities. Granting excessive permissions to users or applications increases the risk of lateral movement if credentials are compromised.
Security vendors such as Palo Alto Networks and Check Point provide cloud security posture management (CSPM) tools that continuously scan cloud environments for misconfigurations and policy violations.
Automation is increasingly essential in addressing configuration risks. Manual oversight becomes impractical in large-scale, multi-cloud deployments. Automated compliance scanning tools detect misaligned policies in real time and generate remediation alerts.
Infrastructure as Code (IaC) practices also help reduce configuration errors. By defining cloud environments programmatically, organizations enforce standardized templates and minimize ad hoc setup processes.
Despite available tools, complexity remains a challenge. Multi-cloud strategies increase operational diversity, requiring teams to manage distinct interfaces and policy structures.
Key factors contributing to cloud misconfigurations include:
- Rapid cloud migration timelines
- Skill gaps in cloud-native security
- Shadow IT deployments
- Insufficient governance frameworks
- Lack of continuous monitoring
Training and governance play a crucial role. Security teams must collaborate closely with DevOps and infrastructure teams to embed secure-by-design principles.
Zero Trust frameworks complement cloud security strategies by limiting access privileges and continuously verifying user identity.
Logging and monitoring capabilities are often underutilized. Comprehensive log analysis helps detect anomalous behavior that may indicate exploitation of misconfigurations.
Regulatory compliance adds additional pressure. Data privacy laws require strict control over how personal data is stored and accessed. Misconfigurations can lead not only to breaches but also to regulatory penalties.
Industry analysts emphasize that cloud security incidents frequently result from operational oversights rather than platform weaknesses.
Continuous posture assessment, automated policy enforcement, and workforce education are essential to reducing exposure.
Cloud adoption continues expanding across enterprises, making secure configuration management a permanent priority.
As digital transformation initiatives evolve, organizations that integrate automated monitoring, standardized templates, and proactive governance into cloud operations significantly reduce risk.
Cloud security misconfigurations may remain a common vulnerability, but disciplined processes and automated controls provide a clear path toward stronger resilience in distributed environments.