As enterprise organizations increasingly rely on SaaS platforms to manage critical operations, security and compliance have become non-negotiable requirements. Unlike consumer software, enterprise SaaS often handles sensitive financial records, employee information, intellectual property, and customer data. Any breach or compliance failure can result in regulatory penalties, reputational damage, and loss of trust.
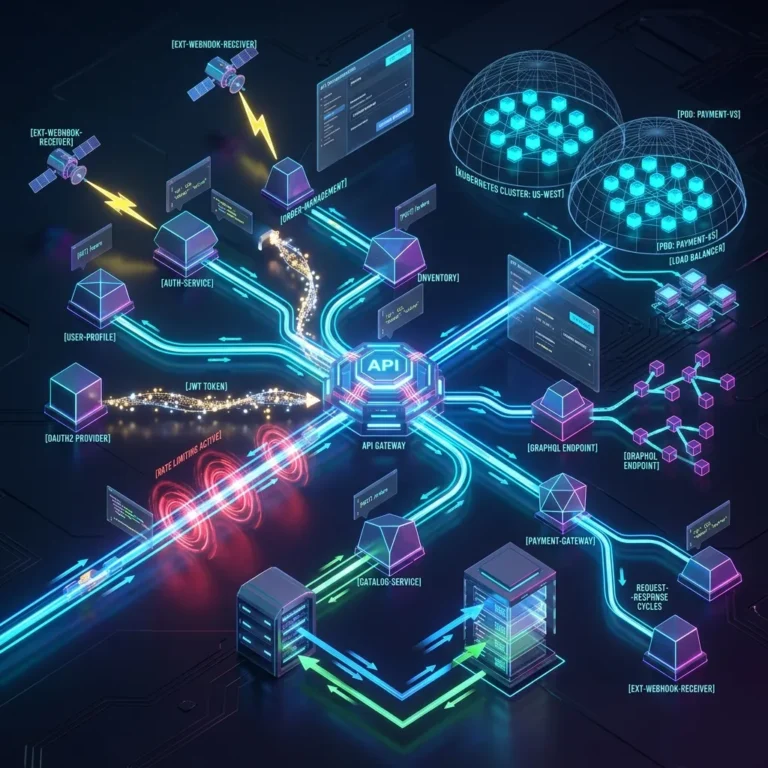
SaaS security operates under a shared responsibility model. The SaaS provider is responsible for securing the infrastructure, application code, and underlying cloud environment. Customers, however, remain responsible for configuring access controls, managing user permissions, and ensuring regulatory compliance within their organization.
Understanding this shared responsibility is fundamental.
At the infrastructure level, SaaS providers rely on secure cloud platforms such as Amazon Web Services and Microsoft Azure. These providers offer physical security, network isolation, encryption services, and compliance certifications. However, the SaaS application layer must still be designed with security embedded from the start.
Application security begins with secure development practices. Code reviews, automated vulnerability scanning, and penetration testing reduce the risk of exploitable flaws. DevSecOps methodologies integrate security directly into development pipelines, ensuring vulnerabilities are addressed before deployment.
Data protection is central to SaaS security. Encryption must be applied both at rest and in transit. Secure transport protocols prevent interception of data during communication between users and servers. Encryption keys must be managed carefully, often using dedicated key management services.
Identity and access management (IAM) plays a critical role. Enterprise customers expect features such as:
- Role-based access control (RBAC)
- Single sign-on (SSO) integration
- Multi-factor authentication (MFA)
- Session management controls
- Detailed audit logging
These controls ensure that only authorized users access sensitive data. Integration with enterprise identity providers simplifies authentication and strengthens governance.
Compliance frameworks further shape SaaS security strategies. Enterprise customers often require certifications such as SOC 2, ISO 27001, or industry-specific standards. Achieving and maintaining these certifications requires formalized security policies, risk assessments, and documented controls.
Data residency is another growing concern. Regulations in certain regions require that data be stored within specific geographic boundaries. SaaS providers must design multi-region architectures that respect these requirements while maintaining performance and redundancy.
Monitoring and incident response capabilities are equally important. Real-time logging and anomaly detection systems identify suspicious activity quickly. Well-defined incident response plans ensure that security events are handled promptly and transparently.
Key components of strong SaaS security include:
- Secure software development lifecycle (SDLC) practices
- Encryption of sensitive data
- Robust identity and access controls
- Continuous monitoring and logging
- Formal compliance certifications
However, security is not purely technical — it is also operational. Employee training, internal access restrictions, and vendor management policies reduce insider risks. Third-party integrations must be evaluated carefully, as external connections can introduce vulnerabilities.
Enterprise procurement teams conduct detailed security reviews before adopting SaaS platforms. They assess documentation, audit reports, and penetration testing results. Transparent communication during these evaluations builds trust and accelerates sales cycles.
Zero Trust principles are increasingly influencing SaaS security architecture. Rather than assuming trust based on network location, every request is authenticated and authorized explicitly. This approach reduces risk in distributed, remote work environments.
Customer trust depends not only on preventing breaches but also on responding effectively if incidents occur. Transparent breach notification policies and clear remediation steps preserve credibility.
Security also intersects with product usability. Overly restrictive controls can hinder productivity. Balancing strong protection with user-friendly workflows requires thoughtful design.
As SaaS adoption continues to grow, attackers increasingly target cloud-based applications. Phishing, credential theft, and API exploitation represent common attack vectors. Proactive defense strategies must evolve continuously.
Ultimately, SaaS security and compliance are foundational to enterprise success. Without strong security posture, scalability and innovation lose relevance.
Enterprise customers entrust SaaS providers with mission-critical data. Protecting that trust requires rigorous security practices, continuous monitoring, and proactive compliance management.
In the cloud-first era, security is not an optional feature — it is the foundation upon which sustainable SaaS growth is built.